Check our terms and conditions, privacy policies, and cookies policy.
Copyright 2024 © All rights Reserved. Designed by LACNet
The nodes in the LACChain networks can be classified into two groups, according to their relevance for the functioning of the network. The two groups are core and satellite nodes. In each of these two groups there are also two different types of nodes, according to the specific tasks they are allowed to perform. Core nodes are classified into validator and boot nodes, and satellite nodes are classified into writer and observer nodes.
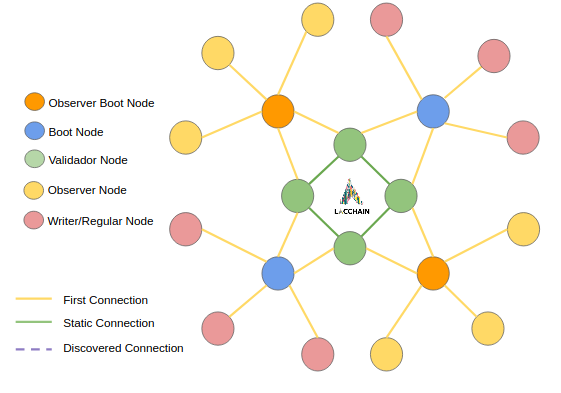
Core nodes play an essential role in the correct functioning of the network. The network can’t work without them. Core nodes are classified into validator and boot nodes.
Validator nodes participate of the consensus protocol. They are responsible for the generation of on new blocks. Validator nodes are only connected to each other and to boot nodes for security and efficiency purposes.
Boot nodes act as a liaison between validator and satellite nodes, which implies that (i) they listen to the writer nodes and pass along to the validator nodes the information about the transactions generated by writers, and (ii) they update the satellite nodes about the new blocks generated by the validator nodes. They are also responsible for setting up new nodes by providing them with a list of active nodes in the network, the latest version of the blockchain, and other relevant information such as whitelists and blacklists. Boot nodes are connected to all the types of nodes in the network.
Satellite nodes do not play an essential role in the correct functioning of the network. The network works without them. Satellite nodes are classified into writer and observer nodes.
Writer nodes can broadcast transactions to the network. They communicate the transactions to the boot nodes, that pass them along to the validator nodes. They can also create private channels between themselves for private communication using the a Private Transaction Manager (e.g., Tessera). Writer nodes are connected to boot nodes and to other writer nodes.
Observer nodes can only read the blockchain. Observer nodes are only connected to boot nodes.
For a P2P network work properly, there must be a good implementation of node discovery that allows a node to discover other nodes in the network. The discover protocol implemented in LACChain Blockchain Networks based on Hyperledger Besu to build the peer to peer network is based on Kademlia.
Kademlia is a well-defined distributed hash table recognized as a robust standard and protocol. LACChain Blockchain Network inherits from Ethereum (the underlying technology of Hyperledger Besu) the use of the discovery part of the Kademlia protocol.
To begin the discovery process, a node needs an identity. The identity of the node is achieved through an enodeID, which is then hashed with keccak into a 256-bit value. For more details, you can go to node identity. Once you have deployed your node and the node has been permissioned in the network, you node will start the discovery process.
The blockchain networks orchestrated by LACNet use UDP protocol to exchange information across the P2P network. The steps to achieve the discovery of nodes in the network are the following:
# Networking
p2p-host="{{node_ip}}"
p2p-port=60606
bootnodes=["enode://ed664ba8ec6959b1b2bd70dce16286cb1688f2f8ab13b8571b0ba4eeb73df9d5f5acb32efff7aabd71fc865d374d2e9c96c524ca543c9aa65dd6543f83852521@35.229.62.151:60606","enode://b10272c5206cd1ec12c6737a41df471e6384cde3e6522a212e3839be09981133eccdacc4ef1c7aacd3aeb63debfa82643d92820bb9f045245cb6badb74dff198@34.138.6.187:60606"]
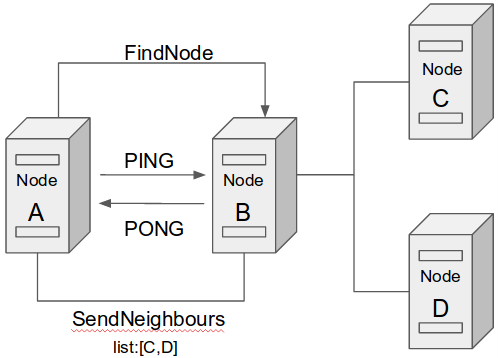
To summarize, the discovery process to join a node to the lacchain network is as follows:
Once discovery is successful, nodes can have peer-to-peer communications over the LACChain Networks based on Hyperledger Besu. Communication consists in sending and receiving messages between nodes. For data transfer, Besu protocol relies on the RLPx Protocol. RLPx enables nodes to transfer encrypted and serialized data through encrypted multiplexed messaging.
This protocol leverages Elliptic Curve Integrated Encryption Scheme (ECIES) to establish secure communications between nodes using public key infrastructure and elliptic curve cryptography. After the handshake, both nodes send to each other which protocols and which versions of these protocols they support: The Ethereum protocol is “eth”, the Ethereum’s Whisper protocol is “shh”, and the Light Ethereum Node Subprotocol is “les”. The subsequent messages are dependent on the protocol chosen.
LACChain Networks based on Hyperledger Besu use IBFT2.0 consensus protocol for the validation of transactions and generation of new blocks. This is a Proof of Authority protocol that eliminate high carbon emissions involved in other consensus protocols such as proof of work. Additionally, all validator nodes in LACChain Mainnets are contractually committed with LACNet to follow certain rules that guarantee the resilience of the network without crypto incentives. For node operators to propose and discuss updates and changes in the LACChain Networks, LACNet coordinates discussion working groups. All of these guarantees that:
In LACChain Networks, validators do not compete to produce blocks, but rather take turns. As such, finality is instantaneous and new blocks are always appended at the end, never rewriting the history. If there were an attack by a majority of validator nodes trying to rewrite the history, any honest node in the network (including validators and not validators) could simply refuse to accept it as soon as the honest node finds that the hash of the block previous to the last proposed block does not match with the hash in the latest version of the chain the honest nodes have.
Additionally, we have developed a protocol to rotate validator nodes in a way that maximizes performance and decentralization.
Despite not yet orchestrated by LACNet, the LACChain Alliance has developed and maintains a Testnet based on EOSIO technology. You can find all the details about it here https://eosio.lacchain.net/en/.
The LACChain Alliance and LACNet are agnostic to blockchain protocols and recognize the benefits of many emerging blockchain protocols. The research team is constantly following these progress and more protocols are expected to be incorporated into the stack of networks orchestrated by LACNet soon.
LACChain Networks are blockchain networks developed by the LACChain Alliance and orchestrated by LACNet. These networks are classified as permissioned public blockchain networks, as defined in the standard ISO/TC 307. As public blockchain networks, LACChain Networks are open to any entity in the world with a special focus on Latin America and the Caribbean. As permissioned networks, all node operators except observer nodes must be authenticated and commit to comply with regulation in order to be permissioned. LACChain Networks have no transaction fees which enables the scalablity of the applications.
There are two types of LACChain Networks orchestrated by LACNet, the Testnets and the Mainnets. The Testnet networks are free. In order to deploy a node, it is required to file a very short registration agreement form as well as reading, understing, and agreeing with the terms of reference. Find the details for the permissioning process here.
The Mainet networks are membership-based. These networks are aimed to ensure relisience and accountability via Service Level Agreements between any entity operating a node and LACNet. Find the details of the permissioning process here.
We are agnostic to blockchain protocols and have already enabled networks using Hyperlderger Besu and EOSIO technologies.
The LACChain Alliance has developed a considerable amount of open-source resources that are available in LACChain’s Github. In this documentation we are only covering those resources that are specifically related to the blockchain networks orchestrated by LACNet. Most of these resources have been migrated from the LACChain Github to LACNet’s Github.
All LACChain Networks comply with the LACChain Framework for Permissioned Public Blockchain Networks developed by the LACChain Alliance. The LACChain Blockchain Framework is a set of recommendations to build neutral, secure, multipurpose, multiprotocol, regulatory compliant, and quantum-resistant blockchain networks The document presents and discusses the concepts of operation, orchestration, and governance. It also addresses topology, routing and connections, block generation, publicness, permissioning, resource distribution, node signatures, quantum-resistance, scalability, monitoring and evaluation, decentralized storage, and private channels. It also tackles regulatory matters.
Check our terms and conditions, privacy policies, and cookies policy.
Copyright 2024 © All rights Reserved. Designed by LACNet